Overview
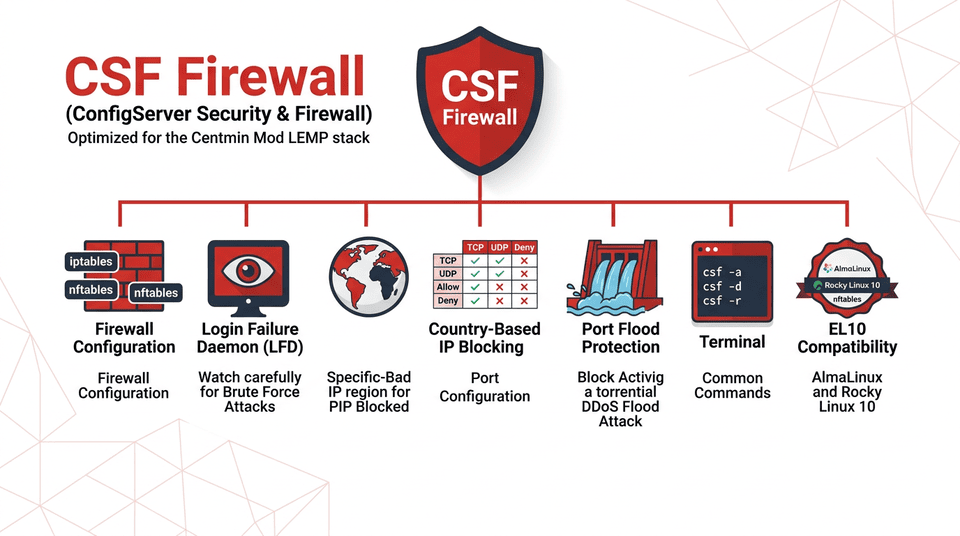
CSF Firewall (ConfigServer Security & Firewall) is a suite of scripts providing firewall security with Stateful Packet Inspection (SPI) and Login Intrusion Detection. It interfaces with iptables to provide a much simpler management experience for server firewall rules.
CSF Firewall is installed by default as part of Centmin Mod v1.2.3 and later. It is highly recommended for all CentOS, AlmaLinux, and Rocky Linux servers running the Centmin Mod LEMP stack.
Key Features
- Stateful Packet Inspection (SPI) firewall via iptables
- Login Failure Daemon (LFD) for brute force detection and blocking
- IPSET support for efficient handling of large IP lists (on KVM/Xen/bare-metal)
- Easy IP allow/deny management via command line
- Dynamic DNS whitelist support for dynamic IP addresses
- Configuration backup and restore profiles
- Self-updating capability
IPSET Support
With Centmin Mod 1.2.3-eva2000.08+, CSF auto-detects IPSET support for more efficient handling of large IP address lists. IPSET is available on dedicated bare-metal servers, Xen, and KVM environments, but not on OpenVZ.
ConfigServer Shutdown Notice
ConfigServer (Way to the Web Ltd) permanently shut down CSF on August 31, 2025. The original configserver.com and download.configserver.com domains are no longer active.
Centmin Mod maintains a self-hosted CSF v15.02 mirror at download.centminmod.com. Running cmupdate automatically switches your installation to the Centmin Mod mirror. CSF continues to work exactly as before with all existing configurations preserved.
EL10 (AlmaLinux/Rocky Linux 10) is still compatible with CSF for now, despite the ongoing nftables transition from iptables.
EL10 Compatibility (AlmaLinux/Rocky Linux 10)
If you have just installed CSF on AlmaLinux 9/10 or Rocky Linux 9/10 and are seeing deprecation warnings in dmesg, the short answer is: CSF works fine. The warnings are informational notices from the kernel, not errors, and they do not affect firewall operation in any way.
CSF v15.02 Confirmed Working on AlmaLinux 10 (March 2026)
All 11 csftest.pl diagnostic tests pass. Both csf.service and lfd.service run cleanly. Firewall rules enforce correctly with 6 active ipset sets. The deprecation warnings in dmesg are expected and do not affect firewall operation.
Live Test Results — AlmaLinux 10
| Check | Result | Detail |
|---|---|---|
| CSF version | ✅ Pass | v15.02 (generic) |
| csf.service | ✅ Pass | active (exited) |
| lfd.service | ✅ Pass | active (running) |
| iptables rules | ✅ Pass | Rules applied and enforcing |
| nft translation layer | ✅ Pass | iptables-nft active, rules visible in nft ruleset |
| ipset | ✅ Pass | 6 sets active (DENY, ALLOW, ALLOWDYN — v4 + v6) |
| csftest.pl | ✅ Pass | 11/11 tests OK |
| IP blocking | ✅ Pass | Block/allow/deny commands working correctly |
| Kernel modules | ✅ Pass | nft_compat, ip_tables, nf_tables, ip_set all loaded |
Verification Commands & Output
Check CSF version:
csf -v
# Output:
csf: v15.02 (generic)Check service status:
systemctl is-active csf lfd
# Output:
active
active
systemctl status csf --no-pager | grep 'Active:'
# Active: active (exited) since ...
systemctl status lfd --no-pager | grep 'Active:'
# Active: active (running) since ...Run the CSF self-test (all 11 tests should pass):
perl /usr/local/csf/bin/csftest.pl
# Output (all tests OK):
Testing ip_tables/iptables
Testing ipt_LOG/LOG
Testing ipt_multiport/multiport
Testing ipt_REJECT/REJECT
Testing ipt_state/state
Testing ipt_limit/limit
Testing ipt_recent/recent
Testing xt_recent/recent
Testing ipt_owner/owner
Testing iptable_nat/DNAT
Testing ip6_tables/ip6tables
RESULT: csf should function on this serverCheck active ipset sets:
ipset list -n
# Output (6 sets active):
chain_DENY
chain_6_DENY
chain_ALLOWDYN
chain_6_ALLOWDYN
chain_ALLOW
chain_6_ALLOWCheck loaded kernel modules:
lsmod | grep -E 'ip_tables|nft_compat|ip_set|nf_tables'
# Output:
nft_compat 32768 160
ip_tables 36864 1 nft_compat
nf_tables 364544 21 nft_compat
ip_set behave 20 nft_compat,ip_set_hash_net,ip_set_hash_ipConfirm the nft translation layer is active (rules managed by iptables-nft):
nft list ruleset | head -5
# Output:
# Warning: table ip filter is managed by iptables-nft, do not touch!
table ip filter {
chain INPUT {
type filter hook input priority filter; policy drop;
}How It Works: iptables-nft
On EL9 and EL10, the system ships iptables-nft instead of the traditional iptables-legacy. When CSF writes rules using the familiar iptables interface, the nft_compat kernel module (shown above with a reference count of 160, meaning 160 CSF rules are currently translated) automatically converts every rule into nftables format behind the scenes. The firewall is fully enforcing — you just have a translation layer in the middle.
About the Deprecation Warnings
The warnings you see in dmesg are kernel notices that certain old-style firewall modules — nft_compat, ip_tables, and ip_set — may eventually be removed in a future OS version. They appear because CSF uses the iptables interface, which on EL9 and EL10 is translated to nftables through the compatibility layer. The same warnings appear on both AlmaLinux 9 and AlmaLinux 10.
Example from AlmaLinux 9.7 (kernel 5.14):
dmesg | grep -i 'deprecated\|will be removed' [ 12.345678] nft_compat: This module is deprecated and will be removed in a future major release. Please use nftables. [ 12.346012] ip_tables: This module is deprecated and will be removed in a future major release. Please use nftables. [ 12.346389] ip_set: This module is deprecated and will be removed in a future major release. Please use nftables.
Example from AlmaLinux 10 (kernel 6.12):
dmesg | grep -i 'deprecated\|will be removed' [ 11.891234] nft_compat: This module is deprecated and will be removed in a future major release. Please use nftables. [ 11.891567] ip_tables: This module is deprecated and will be removed in a future major release. Please use nftables. [ 11.891890] ip_set: This module is deprecated and will be removed in a future major release. Please use nftables.
These are informational notices, not errors. They do not indicate a problem with your firewall. The phrase "future major release" refers to RHEL/AlmaLinux/Rocky Linux 11 or later — not EL10.
On AlmaLinux 9 (supported until May 2032), the warnings are a long-range signal and there is no urgency. On AlmaLinux 10, the same warnings appear and are similarly non-blocking today, though EL10 is likely the last major RHEL release to include the full iptables compatibility shim, making it a longer-term consideration for applications that depend on it.
Centmin Mod EL10 Fix (Applied Automatically)
Since October 2025, Centmin Mod automatically pre-loads 15 required netfilter kernel modules before CSF installation (inc/csfinstall.inc). It also writes a boot persistence config to /etc/modules-load.d/csf-netfilter.conf so the modules are loaded automatically on every reboot.
Running cmupdate on an existing server applies this fix automatically. No manual intervention is required.
Centmin Mod is actively developing native nftables backend support for long-term compatibility beyond EL10. When that work is complete, CSF will write rules directly in nftables format, eliminating the compatibility layer entirely and resolving the deprecation warnings. In the meantime, CSF on EL10 is fully operational and production-ready.
Installation
CSF Firewall is automatically installed during the initial Centmin Mod setup. No manual installation is required — CSF is set up as part of the standard Centmin Mod installation process.
Running cmupdate will pull the latest CSF updates from the Centmin Mod mirror, ensuring your firewall stays up to date after the original ConfigServer shutdown.
CSF is a non-GUI based install when used with Centmin Mod. While CSF supports GUI web interfaces for cPanel, DirectAdmin, and Webmin, Centmin Mod uses command-line management only.
Configuration
The main CSF Firewall configuration file is located at:
/etc/csf/csf.confKey Configuration Files
| File | Purpose |
|---|---|
| /etc/csf/csf.conf | Main configuration file (ports, settings, thresholds) |
| /etc/csf/csf.allow | Allowed (whitelisted) IP addresses and advanced rules |
| /etc/csf/csf.deny | Denied (blacklisted) IP addresses |
| /etc/csf/csf.ignore | IPs ignored by LFD (will not be blocked by login failures) |
| /etc/csf/csf.dyndns | Dynamic DNS hostnames for whitelisting dynamic IPs |
Backup & Restore Configuration Profiles
Centmin Mod 123.09beta01+ automatically backs up the initial CSF configuration after install. You can create your own backup profiles and restore them when needed.
Create a backup:
csf --profile backup-nameList and restore a profile:
csf --profile list
csf --profile restore 1547784956_cmm_after_whitelist
csf -ra
csf -uCommon Commands
CSF provides a straightforward command-line interface for managing your firewall.
| Command | Description |
|---|---|
| csf -r | Restart CSF Firewall (reloads all rules) |
| csf -x | Disable CSF Firewall |
| csf -e | Enable CSF Firewall |
| csf -g <IP> | Search/grep for an IP address in iptables rules and CSF files |
| csf -a <IP> | Allow (whitelist) an IP address |
| csf -d <IP> | Deny (block) an IP address |
| csf -dr <IP> | Remove an IP from the deny list |
| csf -tr <IP> | Remove an IP from temporary ban list |
| csf -td <IP> | Temporarily deny an IP address |
| csf -u | Update CSF Firewall to the latest version |
| csf -ra | Restart CSF and LFD services |
Blocking IP Addresses and CIDR Ranges
Use csf -d to deny (block) individual IP addresses or entire CIDR subnet ranges. Blocked IPs are added to /etc/csf/csf.deny. After blocking, restart CSF with csf -r to apply changes.
# Block a single IP address
csf -d 192.168.1.100
# Block an entire CIDR /24 subnet range (256 IPs)
csf -d 192.168.1.0/24
# Block with a comment for tracking
csf -d 10.0.0.50 "Blocked for brute force attempts"
# Restart CSF to apply the deny rules
csf -rAllowing IPs with Comments
You can add descriptive comments when whitelisting IPs:
csf -a 192.168.1.100 my-office-ipAfter adding an IP to the allow list, reload CSF to apply the changes immediately:
# Reload CSF firewall rules to apply allow/deny list changes
csf -raUnblocking Your Own IP
If your IP gets blocked by CSF, use out-of-band console access (e.g., DigitalOcean Console, Linode Lish, SolusVM Console, or KVM/IPMI) to SSH in and check:
# Search for your IP in CSF rules
csf -g YOUR_IP_ADDRESS
# Remove your IP from the deny list
csf -dr YOUR_IP_ADDRESSLocked Out?
If CSF blocks your IP, you will need out-of-band console access to unblock yourself. Always whitelist your IP in /etc/csf/csf.ignore to prevent LFD from blocking it, and in /etc/csf/csf.allow to whitelist it through the firewall.
Port Configuration
CSF uses /etc/csf/csf.conf to define whitelisted ports for TCP, TCP6, UDP, and UDP6 in comma-separated format. To open or close a TCP port, edit the TCP_IN variable (for inbound) or TCP_OUT (for outbound) — for example, common ports include 22 (SSH), 80 (HTTP), and 443 (HTTPS). After editing, restart CSF with csf -r for changes to take effect.
For example, to open port 8080 for inbound traffic, add it to the TCP_IN list: TCP_IN = "20,21,22,25,53,80,110,143,443,465,587,993,995,8080" then run csf -r to apply. To close a port, simply remove it from the list and restart CSF.
Viewing Current Port Settings
egrep '^TCP_|^TCP6_|^UDP_|^UDP6_' /etc/csf/csf.confThis outputs the port variables controlling inbound and outbound traffic:
| Variable | Description |
|---|---|
| TCP_IN | Allowed inbound TCP ports (e.g. 20,21,22,25,53,80,110,143,443,465,587,993,995) |
| TCP_OUT | Allowed outbound TCP ports (e.g. 20,21,22,25,53,80,110,113,443,587,993,995) |
| UDP_IN | Allowed inbound UDP ports |
| UDP_OUT | Allowed outbound UDP ports |
| TCP6_IN / TCP6_OUT | IPv6 TCP inbound/outbound ports |
| UDP6_IN / UDP6_OUT | IPv6 UDP inbound/outbound ports |
Advanced Port Rules
You can whitelist ports for specific source/destination IPs via /etc/csf/csf.allow. For example, to allow NFS (port 2049) and portmapper (port 111) from IP 11.22.33.44:
tcp|in|d=111|s=11.22.33.44
tcp|in|d=2049|s=11.22.33.44
tcp|out|d=111|d=11.22.33.44
tcp|out|d=2049|d=11.22.33.44
udp|in|d=111|s=11.22.33.44
udp|in|d=2049|s=11.22.33.44
udp|out|d=111|d=11.22.33.44
udp|out|d=2049|d=11.22.33.44For remote Memcached (port 11211) or PHP-FPM (port 9000) servers:
tcp|in|d=11211|s=11.22.33.44
tcp|in|d=9000|s=11.22.33.44
tcp|out|d=11211|d=11.22.33.44
tcp|out|d=9000|d=11.22.33.44After editing, restart CSF:
csf -rSMTP Ports
If using third-party SMTP services, add the appropriate ports (e.g., 465, 587) to TCP_OUT in /etc/csf/csf.conf, then restart CSF.
Country-Based IP Blocking
CSF can block or allow traffic based on country using MaxMind GeoLite2 country code databases — the same shared MaxMind GeoLite2 database source used by the Nginx GeoIP2 module. The difference is that CSF blocks at the firewall/iptables network layer (before requests reach the web server), while Nginx GeoIP2 blocks at the web server/HTTP layer. Nginx GeoIP2 is preferred when your server is behind Cloudflare, because real client IPs reach Nginx but not iptables — making Nginx-level blocking more effective in that scenario. Set CC_DENY in /etc/csf/csf.conf to block countries (e.g. CC_DENY = "CN,RU") and CC_ALLOW to allow specific countries. Both accept comma-separated ISO 3166-1 alpha-2 country codes. After editing, restart CSF with csf -r.
CC_DENY — Block Countries
To deny all traffic from specific countries, edit /etc/csf/csf.conf and set CC_DENY:
# Example: block traffic from CN (China) and RU (Russia)
CC_DENY = "CN,RU"CC_ALLOW — Allow Only Specific Countries
CC_ALLOW works differently — it allows connections from listed countries but still processes all other CSF rules. It does not block unlisted countries by itself.
Applying Changes
After editing the country code lists, restart CSF to apply:
csf -rLF_IPSET: IPSET vs iptables for Large Block Lists
When blocking countries with large IP ranges, CSF uses either IPSET (LF_IPSET = "1" in /etc/csf/csf.conf) or plain iptables rules. IPSET with LF_IPSET enabled is strongly recommended because it stores IP sets in a hash table in kernel memory, making lookups O(1) regardless of set size. With plain iptables, each packet is checked against every rule sequentially, which can severely impact performance and increase CPU usage on VPS instances with limited resources.
Centmin Mod automatically enables LF_IPSET when ipset is available on KVM, Xen, or bare-metal servers. Verify it is enabled in /etc/csf/csf.conf:
# Should be set to 1 (enabled) for efficient country blocking
LF_IPSET = "1"Warning: Do not block Germany (DE)
Blocking DE will prevent CSF from downloading updates from download.configserver.com (now mirrored at download.centminmod.com). On OpenVZ containers, IPSET is not available and country blocking with many iptables rules can consume excessive memory and CPU.
For web-level (Nginx) country blocking as an alternative to firewall-level blocking, see GeoIP2 Lite Module. Nginx-level blocking is useful when behind Cloudflare where client IPs reach Nginx but not iptables. Both CSF country blocking and Nginx GeoIP2 use the same MaxMind GeoLite2 databases as their shared data source for country-to-IP mapping.
For more details and discussion, see the community forum thread.
CSF Port Flood Protection & Pure-FTPD
CSF includes a PORTFLOOD setting in /etc/csf/csf.conf that rate-limits connections to specific ports. The default setting targets FTP (port 21):
PORTFLOOD = "21;tcp;5;300"This means: limit port 21 (FTP) to 5 connections per 300 seconds per IP address. While this protects against FTP connection floods, it can block legitimate FTP uploads when transferring multiple files.
Symptoms
FTP uploads fail or connections drop mid-transfer. You can check if port flood protection is the cause by inspecting system logs:
grep 'Port Flood' /var/log/messagesFix: Increase the Hit Count
Increase the hit count (maximum 20) in /etc/csf/csf.conf to allow more FTP connections per interval:
PORTFLOOD = "21;tcp;20;300"Before making changes, backup your CSF configuration:
csf --profile backup "before-portflood-change"After editing, restart CSF to apply the changes:
csf -raLimit Concurrent FTP Transfers
When uploading many files via FTP, limit concurrent transfers in your FTP client to avoid hitting the rate limit. Even with an increased threshold, too many simultaneous connections can trigger port flood protection.
Per-IP Rate Limiting
The PORTFLOOD setting applies per-IP. If you have multiple users uploading simultaneously, each gets their own limit. Only increase the threshold if legitimate single-user uploads are being blocked.
For more details, see the forum discussion.
Login Failure Daemon (LFD)
The Login Failure Daemon (LFD) is a companion process that runs continuously alongside CSF. It periodically scans log file entries for repeated login failures, responding quickly to brute-force attack patterns by blocking offending IPs.
How LFD Works
- Monitors authentication logs continuously (not via cron) for near real-time response
- Watches commonly abused protocols: SSHD, POP3, IMAP, FTP, and HTTP password protection
- Counts failed login attempts across multiple protocols simultaneously
- When the threshold is reached, LFD forks a subprocess to block the IP via CSF immediately
- Sends email alerts when IP addresses are blocked (enabled by default)
- Logs all activity to
/var/log/lfd.log
Ignoring IPs from LFD
To prevent LFD from blocking a specific IP (e.g., your own), add it to /etc/csf/csf.ignore:
# The following IP addresses will be ignored by all lfd checks
# One IP address per line
# CIDR addressing allowed (e.g. 192.168.254.0/24)
# Only list IP addresses, not domain names
127.0.0.1
YOUR_IP_ADDRESScsf.allow vs csf.ignore
IPs listed in csf.allow are whitelisted through the firewall but can still be blocked by LFD. To fully prevent blocking, also add the IP to csf.ignore.
Integration with Centmin Mod
CSF Firewall integrates tightly with Centmin Mod's LEMP stack to protect all server-facing services.
Default Installation Behavior
- CSF is installed automatically as part of Centmin Mod v1.2.3+ initial setup
- Dynamic DNS support is pre-configured with
DYNDNS=300andDYNDNS_IGNORE=1(1.2.3-eva2000.08+) - CSF auto-updates itself by default on Centmin Mod installs
- Configuration backup profiles are created during initial install (123.09beta01+)
Common Service Scenarios
When connecting to remote servers (SCP, SFTP, rsync), you may need to whitelist the remote server's IP. For remote MySQL connections, also add port 3306 to TCP_OUT.
Whitelisting Dynamic IP Addresses
If you have a dynamic IP from your ISP, use a Dynamic DNS service (e.g., noip.com or DNSExit.com) to create a hostname pointing to your dynamic IP, then add it to CSF:
# Add your dynamic DNS hostname
DYNDNSHOST=yourhostname.publicvm.com
echo "$DYNDNSHOST" >> /etc/csf/csf.dyndns
csf -rWhitelisting Monitoring Services
If you use monitoring services like UptimeRobot, Pingdom, or NodePing, whitelist their IP addresses to prevent CSF from blocking monitoring probes. For example, for UptimeRobot:
# Generate CSF whitelist commands for UptimeRobot IPs
curl -s https://uptimerobot.com/inc/files/ips/IPv4andIPv6.txt | \
while read i; do echo "csf -a ${i}"; doneWhitelisting Cloudflare IPs
If your server is behind Cloudflare, whitelist their IP ranges. You can retrieve the current list via the Cloudflare API:
# Get Cloudflare IPv4 ranges
curl -sX GET "https://api.cloudflare.com/client/v4/ips" | \
jq -r '.result.ipv4_cidrs[]' | sort
# Get Cloudflare IPv6 ranges
curl -sX GET "https://api.cloudflare.com/client/v4/ips" | \
jq -r '.result.ipv6_cidrs[]' | sortCSF Documentation Links
- readme.txt -- Full CSF documentation
- install.txt -- Installation instructions
- changelog.txt -- CSF changelog
- license.txt -- License information
If CSF Firewall is blocking legitimate visitors, check FAQ items 40 & 41 for troubleshooting guidance.